One of the latest sensations in the field of technology could be three-dimensional printing, popularly known as 3D printing. It could be referred to as the practice of producing 3D objects of almost any shape. But before buying one, you should know the uses of 3d printers (or your choice). By doing some research, you can learn the popular ways people use 3D printers. Below are the advantages of 3D printers.
Rapid Prototyping
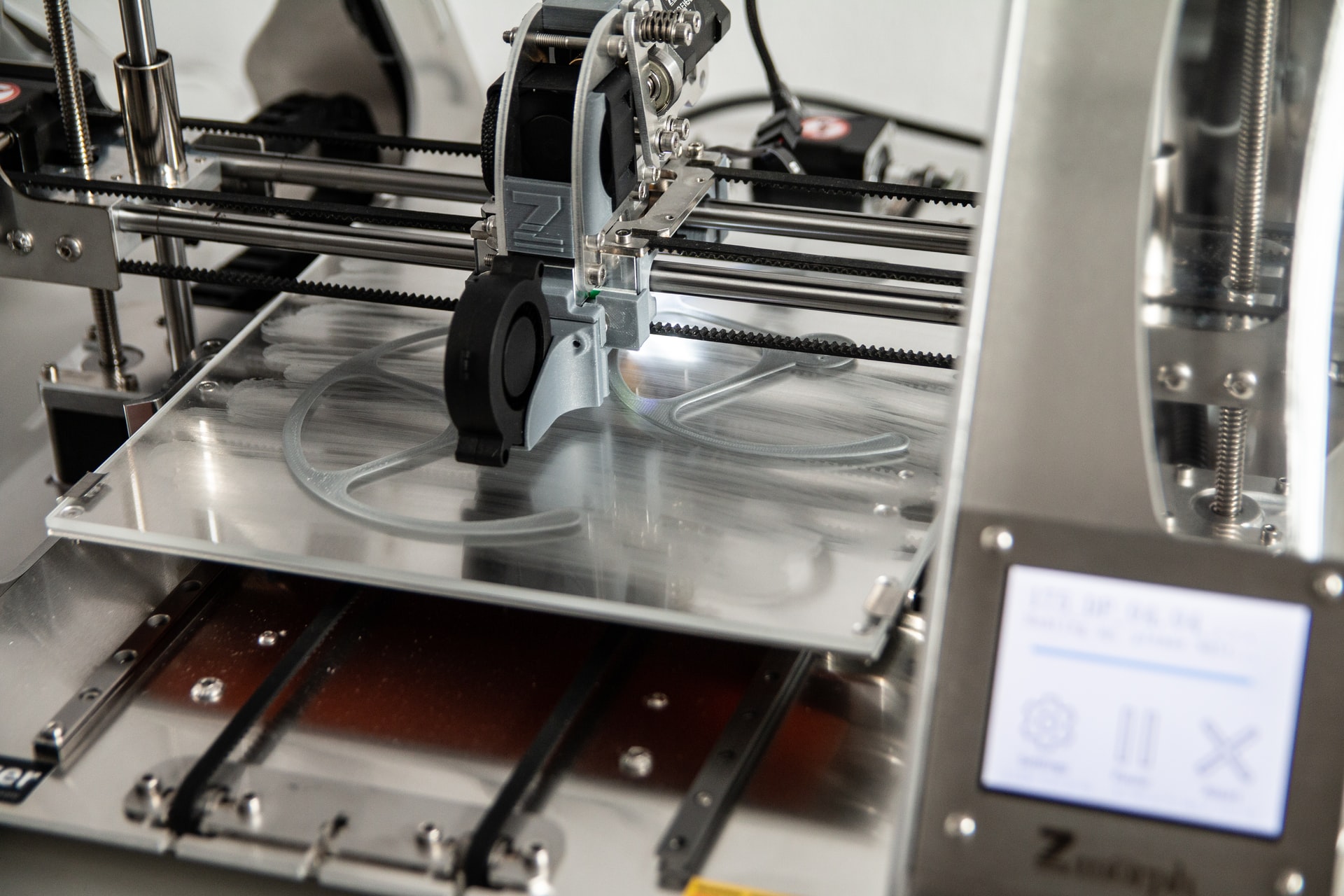
 Basically, a 3D printer could be called an industrial robot that is controlled by a robot and can do the additive process of making a final product compared to the model. It is expected that shortly and in the current issue, more and more people will be able to use 3D printers normally and the people who are not able to handle the printers will be inclined to pay for the services.
Basically, a 3D printer could be called an industrial robot that is controlled by a robot and can do the additive process of making a final product compared to the model. It is expected that shortly and in the current issue, more and more people will be able to use 3D printers normally and the people who are not able to handle the printers will be inclined to pay for the services.
Cost-Effective
 One of the reasons why 3D printers are popular is because they are cost-effective. These possibilities mean a lot of opportunities for interested entrepreneurs. These modern printers could be used in the production of prototypes along with distributed design programs. The possibilities are almost endless and curious people should explore how they can benefit from the advantages along with the expected maturity.
One of the reasons why 3D printers are popular is because they are cost-effective. These possibilities mean a lot of opportunities for interested entrepreneurs. These modern printers could be used in the production of prototypes along with distributed design programs. The possibilities are almost endless and curious people should explore how they can benefit from the advantages along with the expected maturity.
Fast Design and Production
 The entire process of 3D printing starts with a digital file. This is a similar process to 2D printing, where the document is printed after the information has been entered into the computer system. As a result, the term 3D printing can also refer to additive manufacturing, which is a manufacturing process that occurs exponentially. One of the main reasons why many people use this type of printer is because they are fast in designing and production.
The entire process of 3D printing starts with a digital file. This is a similar process to 2D printing, where the document is printed after the information has been entered into the computer system. As a result, the term 3D printing can also refer to additive manufacturing, which is a manufacturing process that occurs exponentially. One of the main reasons why many people use this type of printer is because they are fast in designing and production.
Conclusion
You can get some fantastic brands on the market today. These can be used commercially by the manufacturing process and help the owners or investors to a great extent and thus appreciate the benefits of 3d printers. Entrepreneurs can also decide to buy the machines from the manufacturers and promote them to prevent consumers from profiting. There are a lot of customers available not only locally but also internationally.




 Without communication, we can accomplish virtually nothing. These are just a few of the many ways that email enriches lives around the world. This is the main reason why reverse email lookup is considered timely and welcome, especially as online fraud continues to grow, circumventing the management of many consumers. Email lookup is what most men and women put on whenever they feel uncomfortable with certain messages. To make things easier for everyone, some smart people have created an online directory called reverse email search service. It is a technique that allows email account owners to examine or find out some personal information about those who send them messages.
Without communication, we can accomplish virtually nothing. These are just a few of the many ways that email enriches lives around the world. This is the main reason why reverse email lookup is considered timely and welcome, especially as online fraud continues to grow, circumventing the management of many consumers. Email lookup is what most men and women put on whenever they feel uncomfortable with certain messages. To make things easier for everyone, some smart people have created an online directory called reverse email search service. It is a technique that allows email account owners to examine or find out some personal information about those who send them messages. PPaid email reverse search directories explain the whole idea behind email search methods. Not only are they powerful and reliable, but they help speed up the entire process of distributing unidentified senders online. With the advanced technologies we have today, it is quite easy to find phone numbers of people, homes, businesses, and other associations for our various needs. To locate phone numbers, go online and use search engines to look up a specific person or institution’s contact information. You can click on each number to see more details. To get more search results, you can use websites that specialize in finding phone numbers.
PPaid email reverse search directories explain the whole idea behind email search methods. Not only are they powerful and reliable, but they help speed up the entire process of distributing unidentified senders online. With the advanced technologies we have today, it is quite easy to find phone numbers of people, homes, businesses, and other associations for our various needs. To locate phone numbers, go online and use search engines to look up a specific person or institution’s contact information. You can click on each number to see more details. To get more search results, you can use websites that specialize in finding phone numbers.
 In the constant battle between game developers and hackers, game developers often employ security solutions, such as GameGuard and XignCode. But, hackers also employ various methods to circumvent these security solutions put in place by developers, allowing them unauthorized access and control over game mechanics. The hackers usually go through the use of proxy servers, reverse engineering, and obfuscation techniques.
In the constant battle between game developers and hackers, game developers often employ security solutions, such as GameGuard and XignCode. But, hackers also employ various methods to circumvent these security solutions put in place by developers, allowing them unauthorized access and control over game mechanics. The hackers usually go through the use of proxy servers, reverse engineering, and obfuscation techniques. In this technique, malicious code is injected into the game’s Dynamic Link Library (DLL), allowing the attacker to manipulate the game’s behavior and gain an unfair advantage. To carry out DLL Injection, hackers exploit vulnerabilities in the game’s code or external libraries that it relies on. They inject their own DLL file into the game’s process space, overriding legitimate functions with their malicious counterparts.
In this technique, malicious code is injected into the game’s Dynamic Link Library (DLL), allowing the attacker to manipulate the game’s behavior and gain an unfair advantage. To carry out DLL Injection, hackers exploit vulnerabilities in the game’s code or external libraries that it relies on. They inject their own DLL file into the game’s process space, overriding legitimate functions with their malicious counterparts.